A recently discovered botnet under active development targets Linux systems, attempting to ensnare them into an army of bots ready to steal sensitive info, installing rootkits, creating reverse shells, and acting as web traffic proxies.
The newly found malware, dubbed B1txor20 by researchers at Qihoo 360’s Network Security Research Lab (360 Netlab), focuses its attacks on Linux ARM, X64 CPU architecture devices.
The botnet uses exploits targeting the Log4J vulnerability to infect new hosts, a very appealing attack vector seeing that dozens of vendors use the vulnerable Apache Log4j logging library.
The researchers first spotted the B1txor20 botnet on February 9 when the first sample got trapped by one of their honeypot systems.
In all, they captured a total of four malware samples, with backdoor, SOCKS5 proxy, malware downloading, data theft, arbitrary command execution, and rootkit installing functionality.
DNS tunneling used to conceal C2 comms traffic
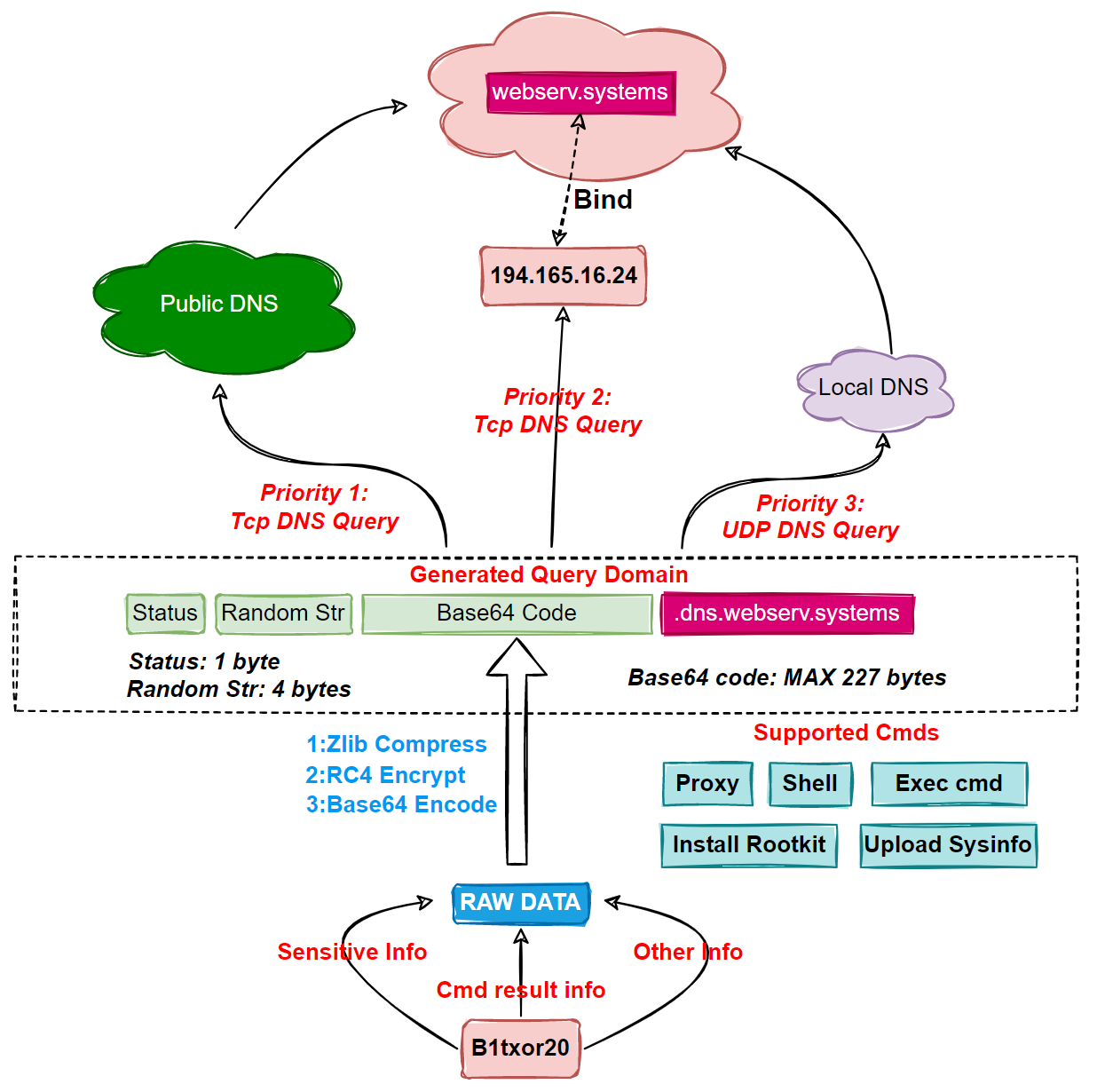
However, what makes the B1txor20 malware stand out is the use of DNS tunneling for communication channels with the command-and-control (C2) server, an old but still reliable technique used by threat actors to exploit the DNS protocol to tunnel malware and data via DNS queries.
“Bot sends the stolen sensitive information, command execution results, and any other information that needs to be delivered, after hiding it using specific encoding techniques, to C2 as a DNS request,” the researchers explained.
“After receiving the request, C2 sends the payload to the Bot side as a response to the DNS request. In this way, Bot and C2 achieve communication with the help of DNS protocol.”
360 Netlab researchers also found that while the malware’s developers included a broader set of features, not all of them are enabled.
This is likely a sign that the disabled features are still buggy, and B1txor20’s creators are still working to improve them and toggle them on in the future.
Additional information, including indicators of compromise (IOCs) and a list of all supported C2 instructions, can be found at the end of the 360 Netlab report.
Ongoing Log4J exploitation by botnets
Since its disclosure, multiple threat actors deployed Log4Shell exploits in their attacks, including state-backed hacking groups linked to governments in China, Iran, North Korea, and Turkey, and as access brokers used by ransomware gangs.
“Since the Log4J vulnerability was exposed, we see more and more malware jumped on the wagon, Elknot, Gafgyt, Mirai are all too familiar,” 360 Netlab researchers added.
For instance, in December, they spotted threat actors exploiting the Log4J security flaw to infect vulnerable Linux devices with Mirai and Muhstik Linux malware.
These botnets were seen “recruiting” IoT devices and servers and using them to deploy crypto miners and perform large-scale DDoS attacks.
Barracuda confirmed 360 Netlan’s report earlier this month, saying they spotted various payloads targeting vulnerable Log4j deployments, with Mirai botnet variants leveraged for DDoS and cryptomining taking the lion’s share.
Comentários