
New malware named HTTPSnoop and PipeSnoop are used in cyberattacks on telecommunication service providers in the Middle East, allowing threat actors to remotely execute commands on infected devices.
The HTTPSnoop malware interfaces with Windows HTTP kernel drivers and devices to execute content on the infected endpoint based on specific HTTP(S) URLs, and the PipeSnoop accepts and executes arbitrary shellcode from a named pipe.
According to a report by Cisco Talos, the two implants belong to the same intrusion set named ‘ShroudedSnooper’ but serve different operational goals in terms of the level of infiltration.
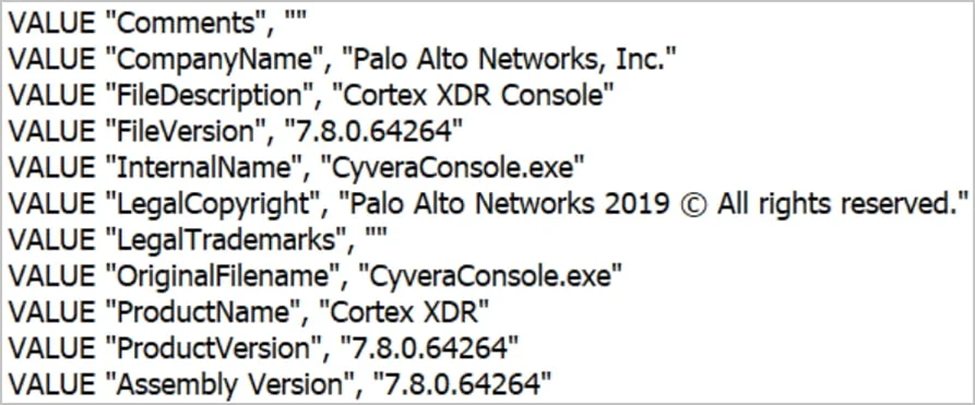
Both implants are masqueraded as security components of the Palo Alto Networks Cortex XDR product to evade detection.
HTTPSnoop
HTTPSnoop uses low-level Windows APIs to monitor HTTP(S) traffic on an infected device for specific URLs. When detected, the malware will decode incoming base64-encoded data from those URLs and run it as a shellcode on the compromised host.
The implant, which activates on the target system via DLL hijacking, consists of two components: the stage 2 shellcode that sets up a backdoor web server through kernel calls and its configuration.
HTTPSnoop establishes a listening loop that waits for incoming HTTP requests and processes valid data upon arrival; otherwise, it returns an HTTP 302 redirect.
The received shellcode is decrypted and executed, and the execution result is returned to the attackers as base64-encoded XOR-encoded blobs.
The implant also ensures no URL clashes with previously configured URLs on the server.
Cisco has seen three variants of HTTPSnoop, each using different URL listening patterns. The first listen for generic HTTP URL-based requests, the second for URLs imitating Microsoft Exchange Web Service, and the third for URLs emulating OfficeCore’s LBS/OfficeTrack and telephony applications.
These variants were sampled between April 17 and April 29, 2023, with the most recent one having the least number of URLs it listens for, likely for increased stealth.
Mimicking legitimate URL patterns from Microsoft Exchange Web Services and OfficeTrack makes malicious requests nearly indistinguishable from benign traffic.
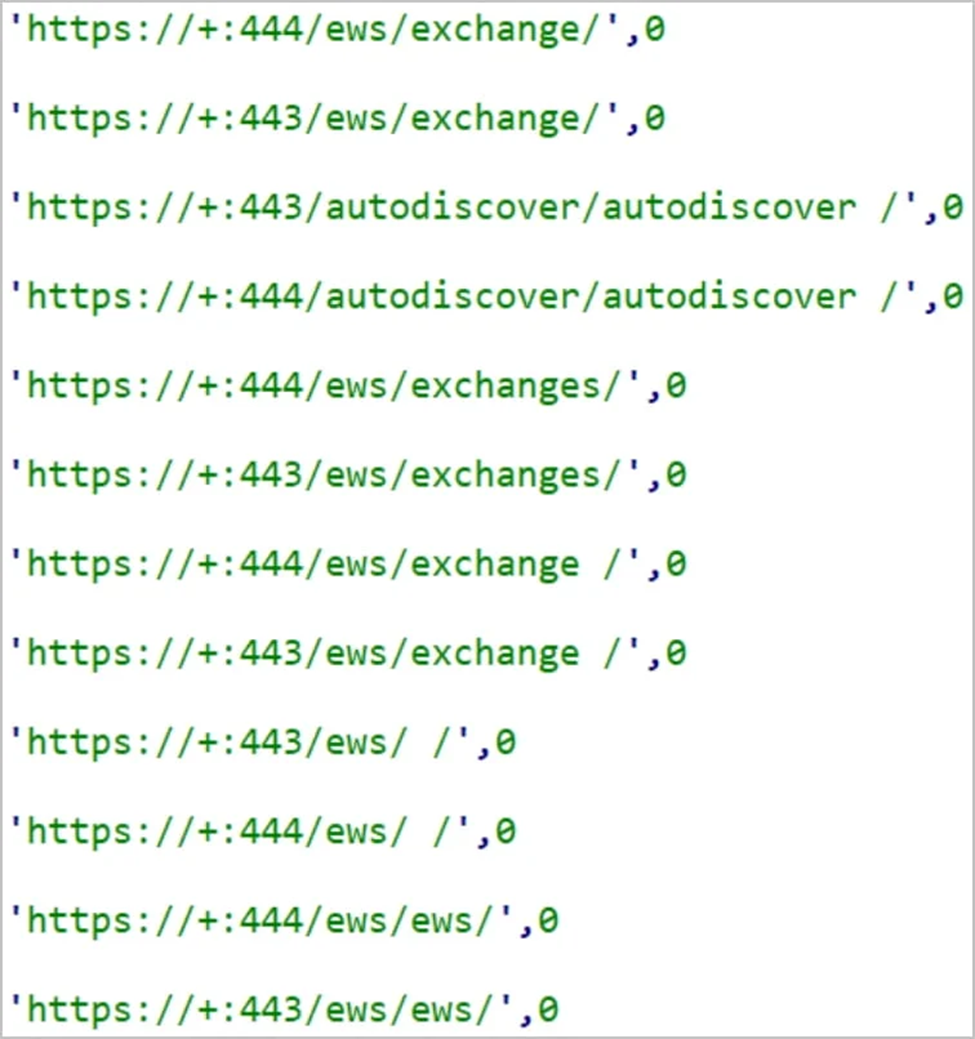
URLs HTTPSnoop is configured to listen for (Cisco)
PipeSnoop
Cisco first spotted the PipeSnoop implant in May 2023, acting as a backdoor that executes shellcode payloads on breached endpoints through Windows IPC (Inter-Process Communication) pipes.
The analysts note that contrary to HTTPSnoop, which appears to target public-facing servers, PipeSnoop is more suited for operations deep within compromised networks.
Cisco also notes that the implant needs a component that supplies the shellcode. However, its analysts haven’t been able to identify it.
Telecommunication service providers often become targets of state-sponsored threat actors due to their crucial role in running critical infrastructure and relaying extremely sensitive information through networks.
The recent surge in state-sponsored attacks against telecom entities underscores the urgent need for enhanced security measures and international cooperation to safeguard them.
Comentários